The Amazon Prime phishing attack that wasn’t…
Earlier this week, we received a moderately believable Amazon Prime phish via email.
The scam had an Account Locked subject line, with a warning that we wouldn’t be able to buy or sell anything via Amazon’s services until we verified our account.
To add a bit more fear and urgency, the crooks went on to warn us that if we didn’t complete the verification process within 24 hours, then our account would be deactivated, not merely suspended.
The “good” news, of course, is that verifying our account was as easy as clicking a link in the email:
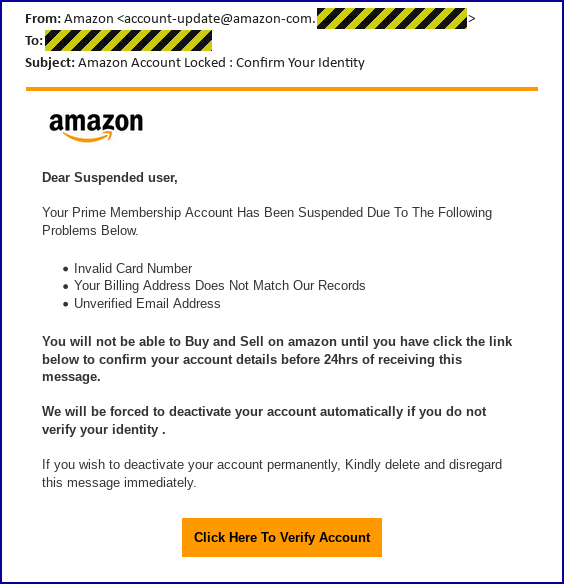
Your Prime Membership Account Has Been Suspended Due To The Following Problems Below:
Invalid Card Number
Your Billing Address Does Not Match Our Records
Unverified Email AddressYou will not be able to Buy and Sell on amazon until you have click the link below to confirm your account details before 24hrs of receiving this message.
We will be forced to deactivate your account automatically if you do not verify your identity.
We don’t think that Naked Security readers would fall for this one, for several reasons:
- There are numerous grammatical and spelling mistakes in the message. We think fluent speakers of English would notice these and be suspicious.
- There’s an unreasonable sense of urgency and drama. Amazon almost certainly wouldn’t use words such as “we will be forced to deactivate your account”, and the company wouldn’t need to deactivate your account for failing to respond within a day. (Online services want to keep you as a customer, not to throw you out!)
- The sender doesn’t know who you are. The greeting “Dear Suspended user” looks, and is, peculiar and suspicious.
- There’s no need to click the link in the email. If the email is a scam, the link will be false. But if the email is true, you can simply go to the Amazon site yourself, or use the Amazon app – the online location of Amazon isn’t a secret. Therefore the correct action is never to click, whether you believe the link or not.
- The link the crooks want you to click uses HTTP. Although an HTTPS link would not mean that the page is safe, you should treat all HTTP links as unsafe – even if you trust the website at the other end – because unencrypted web connections can easily be snooped on by other people.
The teachable moment
Nevertheless, we thought we’d follow the phishing link ourselves, just to see how convincing the final result would be – most phishing sites have some sort of “teachable moment” that we can learn from, no matter how smart we think we are already.
Our first steps were simply to check where the link went, rather than downloading the actual content it linked to.
We found that the first hop was to an otherwise-invisible URL on a legitimate business WordPress site that had obviously been hacked and “borrowed” by the crooks to hide their trail.
The main page of the site was still working normally, promoting a PR business with a (rather ironic) tagline in Spanish saying, “It’s the first impression that counts”:

From here the crooks quietly redirected us to a second hacked site, this time a Middle Eastern company selling awnings, canopies and sun-shades:
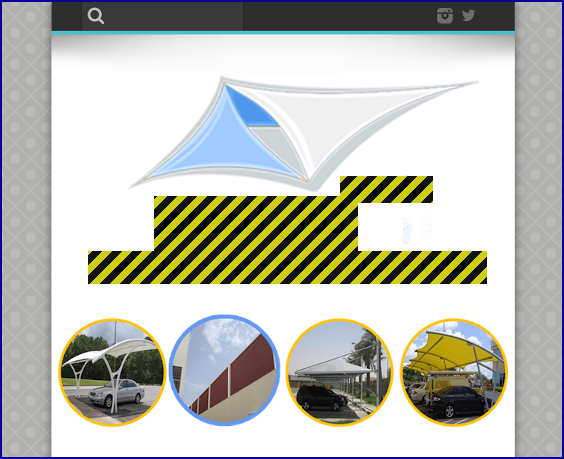
Once again, the crooks didn’t take us to the front door, but instead pointed us at a usually-invisible URL that even the site operator probably wouldn’t notice unless they carefully went looking for files that shouldn’t be there.
And that’s where we got a surprise!
We don’t know whether the crook who sent us the phishing email made a mistake, and used the wrong URL, or whether a second crook had arrived in the interim and then taken over the hacked server from the original hackers…
…but instead of reaching a page that demanded our Amazon password, which is what we expected, we ended up at the crooks’ very own remote access backdoor:
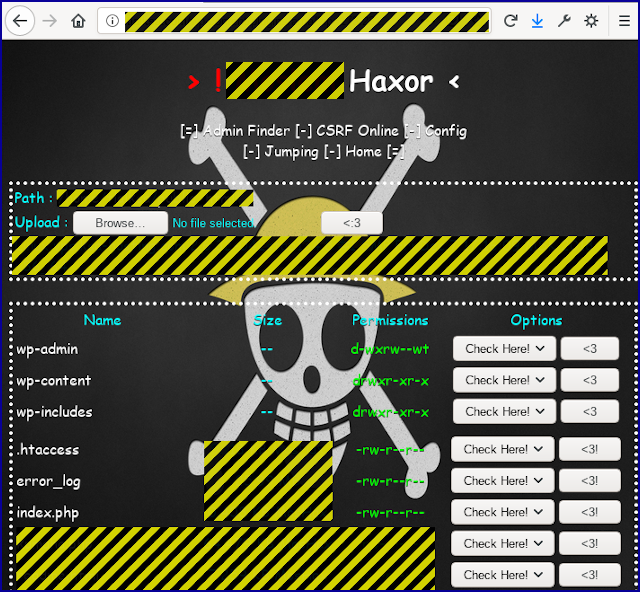
Pirate skull? Check.
Comic Sans font? Check.
Haxor bragging (including the word haxor)? Check.
Emoticons and needless EXCLAMATION POINTS? Check.
Full remote access with no username or password needed? Check.
In this case, by implanting just one PHP file – a scrambled and obfuscated remote access toolkit – at a known URL they could visit later, the crooks gave themslves an unaudited, unsecured, unlimited remote console to the raw files on the WordPress server.
In other words, the crooks have set things up so they can sidestep the WordPress administration console entirely: they don’t need a password; they won’t get logged by the WordPress system; and they can add and modify files that WordPress wouldn’t normally allow, essentially allowing them to hide content such as phishing pages and malware downloads in plain sight.
Worse still, because their access isn’t mediated by the WordPress administration tools, they can also snoop around on the site where even a WordPress administrator might not be able to go, and upload or edit files that WordPress itself would probably prevent.
What to do?
In the end, this turned into a website insecurity story rather than a phishing alert, and it’s a good reminder of several important facts:
- No website is unimportant to the crooks. Cybercrime isn’t just about million-dollar ransomware attacks on giant corporations. Your website has real value to the criminals, even if it’s just as a jumping-off point for them to enable further crimes.
- If your site gets hacked, you’ll probably end up blocklisted. Once the crooks start using your website to host malicious content, you are likely to end up getting blocked or filtered by security products and the major browsers. This could dissuade or even prevent customers from reaching you. So even if the crooks don’t infect your business, they are very likely to affect it.
- Patches and updates are vital. We don’t know how the crooks got access in this case, but a common entry vector to WordPress sites is via plugins that have security holes that you or your hosting provider forgot to patch. WordPress can keep itself up-to-date, but you also need to keep all the other parts of your system, especially your WordPress plugins, up-to-date as well.
You could also consider investing in a network firewall with web filtering capabilities – web protection isn’t just for users inside your network browsing to the outside.
Security products such as the Sophos XG firewall can also guard you from rogue probes and connections from the outside, adding an extra layer of defence against crooks trying to break in.
Lastly, if you are running your own website, whether it’s on a server that belongs to you or via a cloud service at a hosting company, make sure you pick proper passwords, and turn on 2FA for added login protection if you can.
Remember that crooks who get your password and login just once could leave behind a backdoor, like the one shown here, that gives them unfettered, unaudited and almost undetectable access from then on, even if you change your password.
By the way, if you ever do find yourself wandering in through a crook’s backdoor, like we did here, resist the urge, no matter how tempting, to take a look around “for the sake of research” – you could attract the sort of attention you don’t want.
Latest Naked Security podcast
LISTEN NOW
Click-and-drag on the soundwaves below to skip to any point in the podcast. You can also listen directly on Soundcloud.
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/9mSp9ocEk8g/