Apple ships OS X 10.8.5 security update – fixes “sudo” bug at last
 I’m calling it a security update, though it’s officially a full-on point release of OS X Mountain Lion, taking the 10.8 variant of Apple’s OS X to version 10.8.5.
I’m calling it a security update, though it’s officially a full-on point release of OS X Mountain Lion, taking the 10.8 variant of Apple’s OS X to version 10.8.5.
But with twice as many security fixes listed as regular bug fixes and improvements, I’m happy to call it a “security update,” if only in the hope you’ll feel a bit more urgency about deploying it.
There are 15 official security patches, one fix that Apple has appended to the list without explicitly admitting that it was a security issue, and one bonus patch that is mentioned on Apple’s website but not in its emailed security advisory.
I’ll start with the free bonus patch, because I’m delighted it’s happened and I think you should know about it.
The infamous sudo privilege escalation, documented and patched by sudo itself back in February and pointedly exposed on OS X by Metasploit last month, is no more.
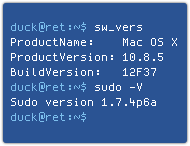 Confusingly, if you run sudo -V to check the version number, you might get the impression it hasn’t been updated, since 1.7.4p6a has the same core version string as the version shipped with 10.8.4 (1.7.4p6).
Confusingly, if you run sudo -V to check the version number, you might get the impression it hasn’t been updated, since 1.7.4p6a has the same core version string as the version shipped with 10.8.4 (1.7.4p6).
Nevertheless, the sudo binary has been updated, and in my tests, the privilege escalation bug had vanished.
Until 10.8.4, doing a sudo -k (which is supposed to deauthenticate you, and thus does not require a password), followed by setting the time to just after midnight on 01 Jan 1970, would give you root access.
In 10.8.5, it does not.
Presumably, Apple yielded to public pressure to fix this long-running hole, but, instead of taking all the sudo changes from the past few months, just backported the sudo -k fix to version 1.7.4p6, a much less risky change.
Moving up the list, the not-a-security-fix I mentioned above is included, almost as an afterthought, as follows:
OS X Mountain Lion v10.8.5 also addresses an issue where certain Unicode strings could cause applications to unexpectedly terminate.
 That’s the bug we decribed as “only six characters from a crash.”
That’s the bug we decribed as “only six characters from a crash.”
Although it probably deserved to be called a denial of service rather than merely “an issue,” it was indeed more of an annoyance than a vehicle for cybercrooks.
At any rate, it’s good to see it patched quickly.
Other significant patches include potential remote code execution holes in:
- JBIG2 decompression in PDF files by the CoreGraphics library.
- JPEG2000 decompression in PDF files by the ImageIO component.
- The web programming system PHP.
- The handling of QuickTime movies by QuickTime.
If you’re an OS X user, you may have been unaware that PHP was installed at all, since it is usually considered a server-side component.
But it is present, and it was vulnerable, although it isn’t enabled by default, even if you turn on OS X’s built-in Apache web server.
PHP isn’t the only server-flavoured component to receive security attention in 10.8.5, with fixes also shipped for the following applications usually found on servers:
- The Apache webserver. (Cross-site scripting.)
- The name server Bind. (Denial of service.)
- The database server PostgreSQL. (Privilege escalation.)
For users on the still-supported earlier versions of OS X, namely Snow Leopard (10.6) and Lion (10.7), the latest fixes come as Security Update 2013-004, rather than as a point release.
The list of fixes for 10.6 and 10.7 is similar to the list for 10.8.5, with the addition of a remote code execution flaw in ClamAV. (ClamAV is not part of the OS X 10.8 distribution.)
Also, the oldest supported OS X version, 10.6, gets a separate update for a remote code execution hole in Safari, which moves to version 5.1.10.
 Neither Lion nor Mountain Lion need or receive this fix, as they are on Safari 6.
Neither Lion nor Mountain Lion need or receive this fix, as they are on Safari 6.
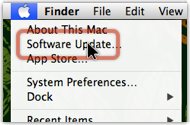
As usual, you can grab Apple’s updates by simply clicking on the Apple Menu and choosing Software Update… or by downloading them as DMG files from Apple’s download site.
Some useful pages on Apple’s site include:
To conclude, even though Macs don’t get malware (only kidding!), Apple has updated its plugin blocker following Adobe’s latest Patch Tuesday.
Safari will now refuse to use Flash plugins earlier than 11.8.800.94.
That doesn’t force you to be bang up to date with Flash – the September Patch Tuesday introduced 11.8.800.168 to fix remote code execution holes in the 11.8.800.94 – but ensuring you are at the latest-but-one is at least a start.
Happy patching!
(I did my 10.8.5 update early this morning: it may be only half a day, but so far, so good.)
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/LwapU0VaBSE/