Bank robbers pose as IT guys, rig device to slurp £1.3m from Barclays
 London’s Metropolitan Police have arrested eight men in connection with a £1.3 million ($2.08 million) bank heist carried out with a remote-control device they had the brass to plug into a Barclays branch computer.
London’s Metropolitan Police have arrested eight men in connection with a £1.3 million ($2.08 million) bank heist carried out with a remote-control device they had the brass to plug into a Barclays branch computer.
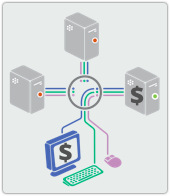
The hardware included a KVM (keyboard, video monitor and mouse) switch and a 3G dongle that enabled the crooks to slurp money from accounts, according to Met Police.
These are legitimate hardware setups: As the police explained, a KVM switch is used in business to enable remote work on computers.
Walking into a bank and pretending to be an IT guy to install such a device is, needless to say, a less legitimate prospect.
Here’s how the crooks pulled off the ruse, according to the Met Police statement:
A male purporting to be an IT engineer had gained access to the branch, falsely stating he was there to fix computers. He had then deployed the KVM device. This enabled the criminal group to remotely transfer monies to predetermined back accounts under the control of the criminal group.
Met Police said that the money was funneled out of the branch, located in the Swiss Cottage district of the north London Borough of Camden, in April.
Barclays Security had actually first reported the £1.3 million loss to police on 05 April 2013.
The report triggered a long-term investigation, led by the Met Police’s Police Central e-crime Unit (PeCU).
As of Thursday, searches were still being carried out across London at addresses where cash, jewelry, drugs, thousands of credit cards, and personal data had already been confiscated.
The eight men, aged between 24 and 47, were arrested in connection with an allegation of conspiracy to steal from Barclays Bank and conspiracy to defraud UK banks.
 Det. Supt. Terry Wilson told the BBC that the police team working the Barclays theft is the same group who’s handling the foiled bank heist plot of Santander—one of the UK’s largest banks—from a week prior.
Det. Supt. Terry Wilson told the BBC that the police team working the Barclays theft is the same group who’s handling the foiled bank heist plot of Santander—one of the UK’s largest banks—from a week prior.
In that recent foiled Santander scheme, the same type of KVM kit came into play.
Using the same modus operandi in both plots, a man had posed as an engineer from a telecoms firm to rig up the device at a Santander branch.
But because police had been tipped off months prior—presumably, the tip was a rather large, £1.3 million-shaped hole in Barclays accounts—the suspects were arrested within hours of the hardware being put into place and before it was turned on.
On Friday, Barclays put out a whopping 72-word statement that stressed how protecting its customers against such malfeasance is priority Numero Uno:
“Barclays has no higher priority than the protection and security of our customers against the actions of would-be fraudsters.
“We have been working closely with the Metropolitan Police following a security breach at our Swiss Cottage branch in April 2013. We identified the fraud and acted swiftly to recover funds on the same day.
“We can confirm that no customers suffered financial loss as a result of this action.”
As security expert Graham Cluley points out, it sounds like the heist can be attributed at least in part to that most human of failings, politeness:
Most of us are guilty of allowing people we don’t recognise to wander around our offices, fiddling with computers, fixing photocopiers, changing the water cooler. Human nature being what it is, we feel uncomfortable questioning people too closely.
Good security training companies know this.
That’s why they send their people into clients’ offices to see what trouble they can get into and, more importantly, whether anybody’s going to stop them, ask for an ID, tell them not to wander around and peer at monitors, and refrain from things like plugging remote-control hardware into computers.
Barclays, get thee to a security training expert!
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/As2sysQS8w0/