Defending against web-based malware: Spot the smoke, don’t wait for fire
 Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage.
Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage.
It’s much the same with cyberattacks: malware rarely gets into your network without signs of smoke beforehand.
Learning to spot smoke, and react accordingly, is not only a smart way to protect your physical property, but a handy metaphor for keeping your network safe, too.
As with fire, there are many ways that malware and other threats can get a foothold in an organization.
That’s why bigger companies have IT staff, firewalls, security policies, anti-virus software, and more. But, even with strong defensive mechanisms, a threat only becomes a problem if it has an opportunity, and opportunity often boils down to a user decision.
Malware is designed to be devious: it searches for ways to circumvent a defensive perimeter. And users can be surprisingly good at finding ways around defensive processes, especially if they feel they get in the way of productivity.
Cybercriminals, of course, exploit this propensity with social engineering: actively persuading users to take shortcuts or to indulge in behaviors that get the attacker past the smoke alarms.
Training users to recognize suspicious on-screen behavior is the best security measure that any family or organization can take. It goes far in curtailing inadvertent participation. It goes beyond policies and mechanisms.
That’s because it doesn’t just prevent inadvertent participation, it recognizes a basic tenet of human nature: security policies and mechanisms are sometimes circumvented when faced with individual authority or sympathy.
Many cyberattacks begin when we do everyday things: check email, browse the web, click on a tempting news story, or agree to some sort of update. They are initiated by activity that should not have been approved.
 With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
Educated users who are knowledgeable of trends and wary of unexpected behavior become your first line of defense. They feel empowered. They are proud to participate in security and they play a more important role in suppressing threats than policies, procedures and technology.
It’s impossible to cover all of the sneaky ways in which malware circumvents suspicion and gains temporary trust – just enough that it can get in the door. But a few simple examples can give users a defensive edge.
So, show users the suspicious signs. Cultivate their antennae. Remind them of the most common hooks used in social engineering. These hooks play either on one of several deep-seated, natural desires such health, wealth, sex and status, or (ironically) on a user’s desire to maintain and even to help improve security.
Here are some examples:
- Trust this brief exception! (Threat poses as important maintenance.)
- Check this out! (Inducement appears to be from a friend.)
- Get more friends! (Appeals to sex, money or personal status.)
- Limited time offer! (Urgency: act fast, or miss out on a bargain.)
- Enjoy life more! (Who doesn’t want greatly enhanced anatomy?)
The interesting thing about these offers is that they create a seductive path between truth and desire. It’s easy to joke about offers for Viagra – after all, who gets lured into these things? – yet Viagra is one of the best selling drugs in the world. So, the key to persuading family or staff to mitigate threats is not to change human nature.
Instead, get them to recognize the risks and to understand that those risks are mitigated the most when they decide to initiate online activities themselves, rather than to be talked into an action by an invitation from a stranger.
Find your own way
Here are a few ways to make sure you are following your own path to an online web destination, rather than being (mis)guided by an outsider:
1. Enter important URLs directly, or use a bookmark.
If you have an account on a website, and you plan to log in, don’t be lazy and use a search engine to get you there: type the full URL into the address bar, or use a bookmark that you previously created. (Many browsers automatically initiate search queries from the address bar if you enter something that doesn’t look like a URL, so be sure to type thecompany.example, not just thecompany.)
Cybercriminals spend plenty of time and money trying to poison search engines so that their malicious sites supplant legitimate ones at or near the top of search results.
2. Look for the HTTPS padlock.
If you plan to do anything that involves logging in, or viewing or uploading information you wouldn’t want anyone in the world to know about, look for “https” (secure HTTP) in the address bar.
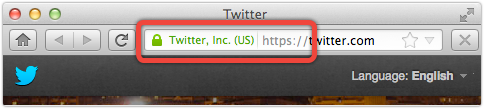
Don’t bother looking for assurances of security and privacy within the actual window, such as pictures of padlocks or mention of cryptographic key lengths. Simply saying something doesn’t make it true.
3. Don’t be influenced by words or images.
It’s common for friends to send links within an email and, personally, I don’t think that it is necessary for organizations to prohibit this sort of email use, or to block links in messages.
But there are some links that we should learn to shun instinctively.
Never use email links to web pages where you have an account, or to any site which requires login. With email, it is difficult to verify the original sender, or to be certain of the integrity of the path between sender and recipient.
Check, and check again
So, when you visit a website where you have an account, follow the advice given in (1) above. When the web page opens, look at the URL again, and follow the advice in (2).
Check that the page is secure (https), and that the domain name is exactly what you expect. Watch out for unfamiliar characters, or a variant of the domain name you are looking for, immediately before the first slash. (E.g. check you are going to bank.example/ and not something like bank.example.198.51.100.12/.)
As with all security threats, alert users are the best prophylaxis against infection. If in doubt, leave it out!
Image of smoke alarm with smoke courtesy of Shutterstock.
Image of pointy click-me hands courtesy of Shutterstock.
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/D6x9HCf6dec/