Hacking Team-derived Flash exploit is now in the wild hijacking PCs
It’s the worst-case scenario of the Hacking Team hack: the as-yet-unpatched Flash vulnerability revealed in the trove of source code leaked from the surveillance-ware company is being exploited in the wild.
Two sources, Malwarebytes and Malware Don’t Need Coffee, have documented updates to the Neutrino exploit kit and Angler exploit kit, respectively. Both kits, which are installed on compromised websites by criminals to infect passing web surfers, now exploit the new Flash bug to execute malicious code on victims’ computers.
Malwarebytes, which had already warned the exploit would be weaponised quickly, notes: “This is one of the fastest documented case of an immediate weaponisation in the wild, possibly thanks to the detailed instructions left by Hacking Team.”
The company shows the exploit working in Firefox:

Malwarebytes’ demonstration of the Neutrino exploit kit in action
Don’t Need Coffee corroborates, showing the Angler exploit kit “successfully exploiting IE11, win7 x64 Flash 18.0.0.194”.
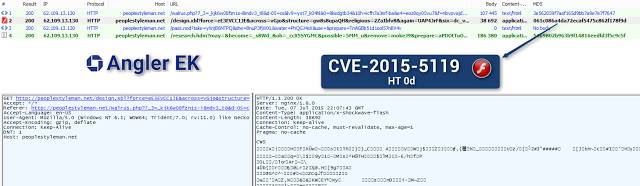
Malware Don’t Need Coffee – Angler exploit kit demonstration
The emergence of the live exploits came to this scribe’s attention via @SwiftOnSecurity:
TRANSLATION: Worst-case scenario is now in play – HT Flash 0day with NO patch is now being used to deliver Cryptolockers via exploit kits
— InfoSec Taylor (@SwiftOnSecurity) July 8, 2015
[!] ACTION REQUIRED: Set Flash as Click to Play in all your browsers. Here’s easy all-in-one guide via @howtogeek | http://t.co/8IMLeW09nx
— InfoSec Taylor (@SwiftOnSecurity) July 8, 2015
[!] ACTION REQUIRED: Set Flash as Click to Play in all your browsers. Here’s easy all-in-one guide via @howtogeek | http://t.co/8IMLeW09nx
— InfoSec Taylor (@SwiftOnSecurity) July 8, 2015
Adobe expects its fix to land on July 8. ®
Sponsored:
Hyper-scale data management
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2015/07/08/hacking_teamderived_0day_is_now_in_the_wild/