It’s May 2. Know what that means? Yep, it’s the PR orgy that is World Password Day… again
If there’s anything worse that having to constantly come up with and enter passwords, it’s the idiotic way in which we all do it.
Yep, it’s World Password Day again and that means one thing: companies of every hue and shade politely but firmly telling us we’re a disgrace.
Avast, for example, let us know that “unfortunately, many people around the world – including 83 per cent of Americans – use weak passwords that are easy to crack.” That’s right more than 8 out of 10 people haven’t got the loudly shouted message. An unfortunate side-effect of this: there will never be an end to World Password Day.
Having established we’re all idiots, Avast – which, surprise surprise, sells security software – points out that 25 per cent of people have never – yes, never – changed their passwords. So that the two main messages about passwords, namely:
- Choose complex ones, and
- Change them every so often
…flushed right down the toilet.
In addition to Avast, there is no shortage of companies pointing out that having bad passwords is not the equivalent of getting takeout when you should really cook but can’t be bothered – it’s actually a big problem.
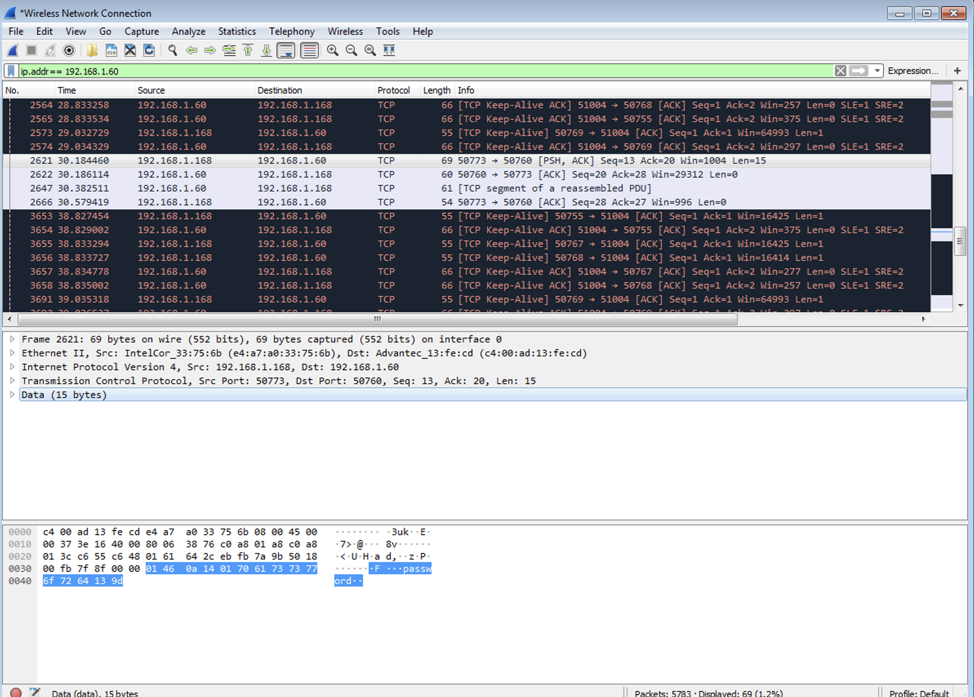
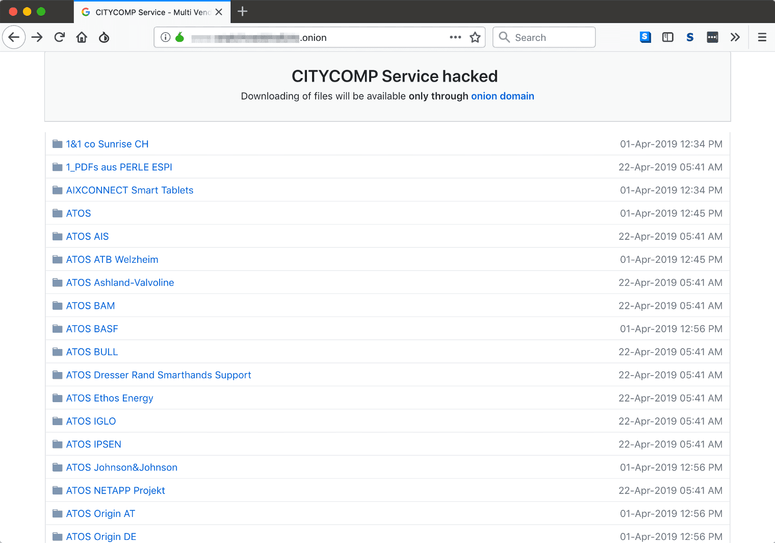
There have been an unprecedented number of massive data breaches in recent years where tens of millions of people’s usernames and passwords have been stolen – and are readily traded online. If you are still using that same password on another site, you are a sitting duck – and pretty much everyone is scrambling to deal with stolen ID crimes as a result.
Here’s another company – SecureAuth – pointing out that 81 percent of confirmed data breaches still involve weak, default or stolen passwords.
Blame spreading
Of course, people are smart and have checked whether their email address has been involved in a big data breach – using sites like Haveibeenpwned.com. No, of course they haven’t: 58 per cent of Americans have never checked according to Avast – and bear in mind that Avast surveyed its own users, people who have gone to the trouble of paying for security software.
But before you sysadmins start getting smug about how you use a password manager like 1Password and would never be caught up with your password pants down, we have some sobering news for you too.
OneLogin has yet more worrying stats: two-thirds (65 per cent) of sysadmin don’t check employee passwords against common password lists and more than three-quarters (75 per cent) of you don’t check employee passwords against password complexity algorithms.
Yes, that’s right – you are part of the problem. And while you can expect everyone to bitch and moan about having to come up with complex passwords, that’s also your job: an employee is likely using the same password for your internal systems as they are for Instagram.
According to OneLogin, 63 per cent of network administrators don’t require special characters or minimum length passwords. Numbers? 71 per cent don’t require it. Upper and lowercase? 72 per cent. And an amazing 63 per cent have not put password rotation policies in place. What are you doing people?
Ok, we know what you’re doing. The same data dump points out that sysadmins waste two-and-a-half months every year resetting internal passwords. Janice may not realize how ridiculously easy it is to crack her clever “qwerty” password but at least you don’t have to deal with her every single Monday when she’s forgotten the complex one you “made” her come up with.
But you don’t away with it that easily: 96 per cent of financial institutions still rely on legacy setups that tie usernames and passwords to authentication, according to OneSpan. And that is despite the fact that 44 per cent of account takeovers come from username/password combinations exposed in data breaches.
The answer!
There is hope of some sort: according to OneSpan, 60 per cent of those that it surveyed (“300 IT decision makers across the US,” apparently) “plan to invest in new multifactor authentication technologies in 2019, including biometrics and AI/machine learning.”
We wonder though whether that “plan to invest” is contingent on you getting the expanded budget you put in for this year. Which, let’s be honest, we all know you are not getting and that if you did you’ll spunk the money you could have spent on 2FA on that new server that you really don’t need.

Android apps prove a goldmine for dodgy password practices
But let’s get on to the inevitable closing part of World Password Day: what’s the solution? And guess what? Yes, it’s a password manager. For, like, the 50th year running.
But we have some other notable suggestions. Unisys reckons “maybe it should be called National PassPHRASE day! It’s the WORD in PassWORD that is one thing holding people back.”
It’s a fair point. But it’s like trying to get people to say “vacuum cleaner” instead of “Hoover” or “sticking plaster” instead of “Band-Aid.” Spackle. Google. Password. It ain’t gonna happen.
Here’s Rod Simmons, VP of Stealthbits trying his hand: “After three decades of IT tormenting users about creating complex passwords then forcing them to come up with a new one ever 60-90 days for some random sadistic reason…”
A strong start, we’re sure you’ll agree. What is Rod’s solution? NIST advice – specifically NIST 800-63b. He loves it. “What is great about the new guidance? Three benefits: 1) Only change passwords if there is sign or compromise or it is in a compromise dictionary; 2) Stop time-based password expiration; and 3) Relax complexity rules.”
Hang on. Those last two are what everyone else has just been ragging on everyone else for NOT doing.
The real answer to passwords? Get rid of them altogether, says co-founder of Cequence Security, Ameya Talwalkar: “We hope to live in a password-less world, one day. Until then, protect yourself with few good habits:
- Do not use the same password across multiple sites.
- Use biometric authentication on mobile phone apps
- Use at least two online password managers to securely save and sync your credentials
- Change passwords on finance and healthcare related applications on a regular basis.”
So there you go – the answer this year isn’t just a password manager. It’s TWO password managers!
And with that, we’ll give up giving contradictory and impossible advice for another year and going for a pint or six. ®
PS: We recommend multi-factor authentication, use unique per-website long pass phrases and a password manager if necessary, and change passwords if they are stolen.
Sponsored:
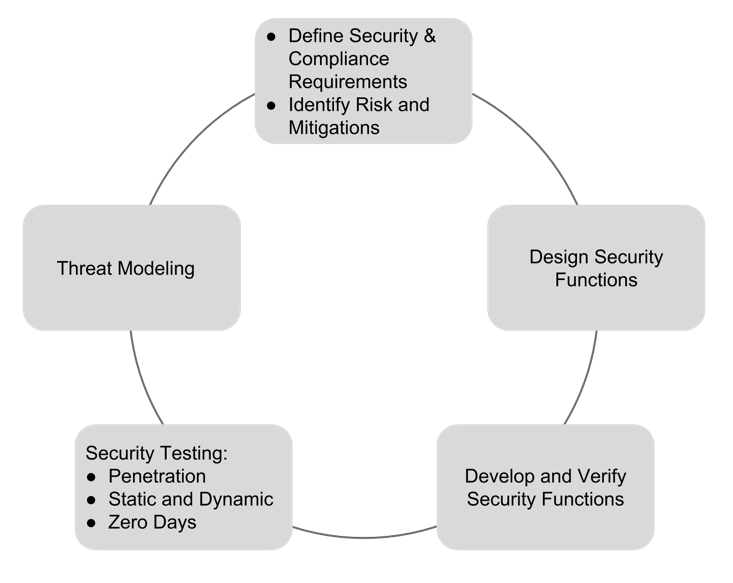
Becoming a Pragmatic Security Leader
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2019/05/02/world_password_day/