After months-long, cross-border investigations, Europol announced on Friday that it’s arrested more than two dozen people suspected of draining bank accounts by hijacking victims’ phone numbers via SIM-swap fraud.
Following a ramp-up in SIM-jacking over recent months, police across Europe have been gearing up to dismantle criminal networks that organize these attacks, Europol says.
That growth mirrors what’s happening in the US: In October, the FBI warned that bad guys were getting around some types of two-factor authentication (2FA). The easiest – and, therefore, the most common – way to sneak past 2FA is SIM-swap fraud, where an attacker convinces a mobile network (or bribes an employee) to port a target’s mobile number or plants malware on a victim’s phone, thereby allowing them to intercept 2FA security codes sent via SMS text.
How the crooks swing a SIM swap
As we’ve explained, SIM swaps work because phone numbers are actually tied to the phone’s SIM card – in fact, SIM is short for subscriber identity module, a special system-on-a-chip card that securely stores the cryptographic secret that identifies your phone number to the network.
Most mobile phone shops out there can issue and activate replacement SIM cards quickly, causing your old SIM to go dead and the new SIM card to take over your phone number… and your telephonic identity.
That comes in handy when you get a new phone or lose your phone: your phone carrier will be happy to sell you a new phone, with a new SIM, that has your old number.
But if a SIM-swap scammer can get enough information about you, they can just pretend they’re you and then social-engineer that swap of your phone number to a new SIM card that’s under their control.
By stealing your phone number, the crooks start receiving your text messages along with your phone calls, and if you’ve set up SMS-based two-factor authentication (2FA), the crooks now have access to your 2FA codes – at least, until you notice that your phone has gone dead, and manage to convince your account providers that somebody else has hijacked your account.
Europol’s announcement came after the fruition of two operations targeting SIM hijackers: Operation Smart Cash, and Operation Quinientos Dusim.
Operation Quinientos Dusim
In January, Europol investigators teamed up with Spanish police to target suspects across the country whom they suspected were part of a hacking ring that stole over €3 million (USD $3.35m, £2.74m) in a series of SIM-swapping attacks. They arrested a dozen people: five in Benidorm, six in Granada and one in Valladolid.
The suspected SIM-jackers were between the ages of 22 and 52 and hailed from Italy, Romania, Colombia and Spain. Europol says the gang hit over 100 times, stealing between €6,000 (£5,480, USD $6,700) and €137,000 (USD $152,880, £125,210) per attack from bank accounts of unsuspecting victims.
Europol says the suspects’ modus operandi was simple: they allegedly got their victims’ online banking credentials by a variety of malware, including banking Trojans. Once they had the credentials, the suspects allegedly applied for a duplicate of the victims’ SIM cards by showing fake documents to the mobile service providers. After they got the duplicate SIM cards, they could transfer funds out of their victims’ accounts by intercepting the 2FA codes sent via SMS to the rightful account owners’ phone numbers on file.
Whoosh! went the bank accounts’ balances, transferred over to bank accounts controlled by the SIM-jackers’ money mules in the blink of an eye. Europol said the whole thing took between 1 to 2 hours: just about as much time as it would take for a victim to realize that their phone number wasn’t working any more.
Operation Smart Cash
The second operation, Operation Smart Cash, was an eight-month, joint project between police from Romania and Austria, with support from Europol. The ultimate results: the arrest of 14 people who were allegedly part of another SIM-swap attack gang.
Earlier in February, investigators arrested the suspects in simultaneous raids throughout Romania.
Europol says that this gang’s thefts targeted dozens of victims in Austria. The alleged crooks carried out the thefts through a series of SIM-swapping attacks in the spring of 2019.
After they got their clutches on a victim’s phone number, the alleged SIM-jackers would then use stolen banking credentials to log onto a mobile banking app to generate a transfer, which they then validated with a one-time password sent by the bank via SMS. Next, this gang allegedly had its members withdraw the money at cardless ATMs.
The gang managed to steal over half a million euros, Europol says (£456,975, USD $558,350).
What to do?
Whether they’re breaking into regular old bank accounts or Bitcoin accounts, the crime is obviously extremely costly for the victims who watch helplessly as their accounts drain.
So, here are our tips:
- Watch out for phishing emails or fake websites that crooks use to acquire your usernames and passwords in the first place. Generally speaking, SIM swap crooks need access to your text messages as a last step, meaning that they’ve already figured out your account number, username, password and so on.
- Avoid obvious answers to account security questions. Consider using a password manager to generate absurd and unguessable answers to the sort of questions that crooks might otherwise work out from your social media accounts. The crooks might guess that your first car was a Toyota, but they’re much less likely to figure out that it was a
87X4TNETENNBA.
- Use an on-access (real-time) anti-virus and keep it up-to-date. One common way for crooks to figure out usernames and passwords is by means of keylogger malware, which lies low until you visit specific web pages such as your bank’s login page, then springs into action to record what you type while you’re logging on. A good real-time anti-virus will help you to block dangerous web links, infected email attachments and malicious downloads.
- Be suspicious if your phone drops back to “emergency calls only” unexpectedly. Check with friends or colleagues on the same network to see if they’re also having problems. If you need to, borrow a friend’s phone to contact your mobile provider to ask for help. Be prepared to attend a shop or service center in person if you can, and take ID and other evidence with you to back yourself up.
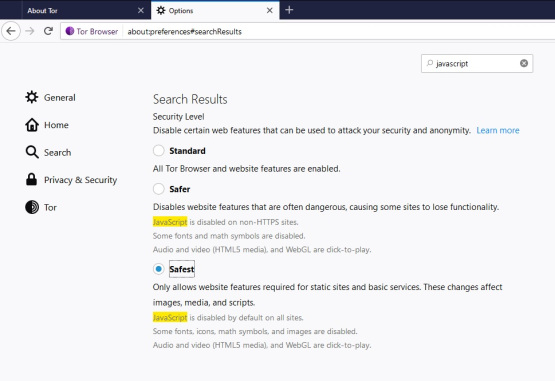
- Consider switching from SMS-based 2FA codes to codes generated by an authenticator app. This means the crooks have to steal your phone and figure out your lock code in order to access the app that generates your unique sequence of login codes.
Having said that, Naked Security’s Paul Ducklin advises that we shouldn’t think of switching from SMS to app-based authentication as a panacea:
Malware on your phone may be able to coerce the authenticator app into generating the next token without you realizing it – and canny scammers may even phone you up and try to trick you into reading out your next logon code, often pretending they’re doing some sort of “fraud check”.
Latest Naked Security podcast
LISTEN NOW
Click-and-drag on the soundwaves below to skip to any point in the podcast. You can also listen directly on Soundcloud.
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/ORrtEW70IY8/

 Check out
Check out  Check out
Check out  Check out
Check out