Firefox burns Chrome in our trustworthy browser poll
About a month ago I asked Naked Security readers Which web browser do you trust? Your answer was emphatic: it’s Firefox.
 I asked this question because trustworthiness has become an important selection criteria for web browsers and there is no objective test for it.
I asked this question because trustworthiness has become an important selection criteria for web browsers and there is no objective test for it.
Modern web browsers are mature and complex products and, despite inflated version numbers and conspicuously busy release cycles, their feature sets evolve quite slowly.
Selecting the right web browser is no longer a question of what the software can do, it’s about whether or not it can do the things we expect it to do quickly, securely and with due regard for our privacy.
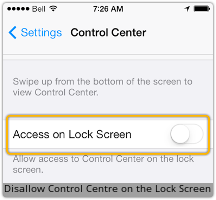
Our poll offered readers the chance to vote for one of the six most popular web browsers – Chrome, Firefox, Internet Explorer, Opera, Safari and Chromium – and asked which you trusted the most.
Mozilla’s Firefox, the linear descendant of both Netscape Navigator and the original ‘graphical web browser’ the NCSA Mosaic, was a runaway winner.
Firefox accrued almost double the number of votes of its nearest rival, Google Chrome, and more than six times the votes awarded to perennial rival and fellow ‘browser wars’ veteran Internet Explorer.
The results are even more emphatic when you consider how many people actually use each browser.
Below is a table that compares the number of votes each browser received in the poll against the number of unique article pageviews from each of those browsers over the same period.
Results are ranked in order of conversion rate – the rate at which page views by a given browser correlate with votes for that browser (Chrome and Chromium identify themselves in the same way and we can’t separate their unique page views so their results are combined in this table).
Top of the table is Opera which was the only browser that scored more votes for trustworthiness than it had users, although it did so with much smaller totals than its competitors.
You could probably sum up the entire history of the Opera browser with the phrase “small but loyal following” and despite the regard in which its users hold it Opera seems destined to remain the perennial bridesmaid of the browser world.
The poor showing of Internet Explorer is notable but perhaps not surprising given that it is often imposed on users as a matter of corporate policy.
What stands out at me is the difference between the Mozilla and Google products. Both browsers are well established and well known open source projects, they both run on Windows, Mac and Linux and unlike Explorer or Safari neither come bundled with an operating system.
Perhaps Chrome users are more cynical or more realistic about where they place their trust. Or perhaps people who choose Chrome are also people who don’t vote in internet polls.
We don’t know but I suspect, as the comments on our poll seem to suggest, that the reason for Chrome’s poor showing is that Google’s claim to Do No Evil is simply no longer convincing.
The untrustworthiness of Google is a consistent theme across the most highly rated comments on the poll:
frankly I trust Google the least, as they have too many data points for comparison.
I don’t trust Google as far as I could throw ’em. As a company, it’s entirely uninterested in my security or privacy, especially if it can make money by selling my personal information.
Trusting any software completely is a bit foolish, but anyone who actively trusts Chrome is a good subject for psychological study.
You get the idea.
Of course this is only an online poll and and not a scientific experiment so my conclusions should be taken with a liberal pinch of salt.
Let me know what you think in our comments below.
Follow @NakedSecurity
Follow @MarkStockley
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/sOZNmpeQ9a4/
 The biometrics team of Germany’s well-known Chaos Computer Club (CCC) claims it has
The biometrics team of Germany’s well-known Chaos Computer Club (CCC) claims it has 
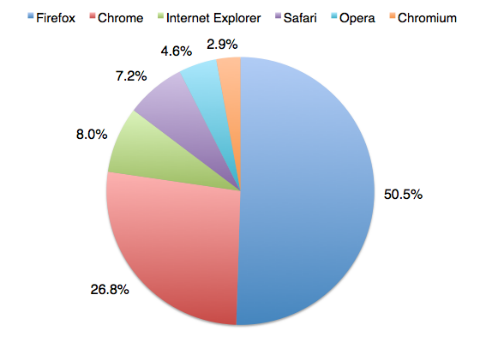
 Another iOS 7 lockscreen bypass has surfaced.
Another iOS 7 lockscreen bypass has surfaced.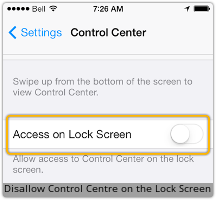
 The biometrics team of Germany’s well-known Chaos Computer Club (CCC) claims it has
The biometrics team of Germany’s well-known Chaos Computer Club (CCC) claims it has 
 Another iOS 7 lockscreen bypass has surfaced.
Another iOS 7 lockscreen bypass has surfaced.