European Commission calls for single privacy law in wake of PRISM snooping
 Europe needs new cross-national data protection laws in order to restore trust in the data-driven economy.
Europe needs new cross-national data protection laws in order to restore trust in the data-driven economy.
That’s according to Viviane Reding, vice president of the European Commission and EU commissioner for justice.
Speaking to delegates at the European Data Protection Conference in Brussels, she said:
Trust in the data-driven economy, already in need of a boost, has been damaged. This is a source of concern because of the potential impact on growth. Collected, analysed and moved, personal data has acquired enormous economic significance. According to the Boston Consulting Group, the value of EU citizens’ data was €315 billion in 2011. It has the potential to grow to nearly €1 trillion annually in 2020.
Trust has been lost
Reding said that restoring trust and growth were both imperative and that they could be delivered at the same time through the European Union’s data protection reform. This, she said, “will restore the trust of EU citizens by putting them back in control of their data” and, secondly, will, “boost growth through opening the European Union’s market in data.”
“Trust has been lost in all these spying revelations. They are particularly damaging for the digital economy because they involve companies whose services we all use on a daily basis,” she said.
Reding acknowledged that PRISM, the US data gathering surveillance program, had a large impact on the erosion of trust but noted that:
Trust in the data driven economy began to fall long before the first NSA slides were published. The data protection reform proposed by the Commission in January 2012 provides a response to both these issues: to Europeans’ concerns about PRISM as well as the underlying lack of trust.
Using cloud computing as an example Reding said, “trust is bankable,” as she detailed how American spying revelations had left 56% of the respondents to a Cloud Security Alliance survey declaring hesitance to work with any US-based cloud service providers.
“The Information Technology and Innovation Foundation estimates that the surveillance revelations will cost the US cloud computing industry $22 to $35 billion in lost revenues over the next three years,” she said, whilst making the point that EU cloud providers, operating under a higher standard of data protection, would be able to deliver a much more compelling selling advantage.
Safeguarding data protection
Reding said that such figures highlight the need for change in European governments’ approach to data protection and she drew attention to safeguards that the Union can employ:
First, territorial scope. The Regulation makes clear that non-European companies, when offering goods and services to European consumers, will have to apply the EU data protection law in full. European rules should apply from the moment of collection to the moment of deletion of the data.
Second, international transfers. The Regulation establishes the conditions under which data can be transferred from a server in the EU to a server in the U.S. It is the transfer of data outside the EU which brings it within the reach of the NSA.
Third, enforcement. The new rules provide for tough sanctions (up to 2% of a company’s annual global turnover) to make sure that companies comply with EU law. At the moment, when confronted by a conflict between EU and foreign law, foreign companies have no reason to hesitate. In future, they will think twice.
Fourth, processors. The Regulation includes clear rules on the obligations and liabilities of cloud providers who are processors of data. As PRISM has shown, they present an avenue for those who want to access data.
Reding also made the point that current data protection regulations are overly bureaucratic in nature and need simplifying into one set of rules that would be consistently applied across the region.
She noted how a company that trades in all 28 Member States may have to navigate and comply with 28 different laws, some of which are both long and complex. In Germany, for example, their own interpretation of EU data protection law is some 60 pages in length.
[If you] take those 60 pages and multiply by 28 Member States. Then you’ll get an idea of what the term ‘regulatory complexity’ means in practice. A mountain of red-tape which has an enormous cost.
Proposals to reform data protection rules within the European Union have been debated for the last two years. Now, perhaps, an accord will be struck between Members as they look to protect citizens from unwanted surveillance.
Follow @Security_FAQs
Follow @NakedSecurity
Image of padlock courtesy of Shutterstock.
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/DEn4XRxjRLg/

 Happy day, USA: When we click “Like” on Facebook, we are now constitutionally protected from getting fired!
Happy day, USA: When we click “Like” on Facebook, we are now constitutionally protected from getting fired!  Serial iOS
Serial iOS 
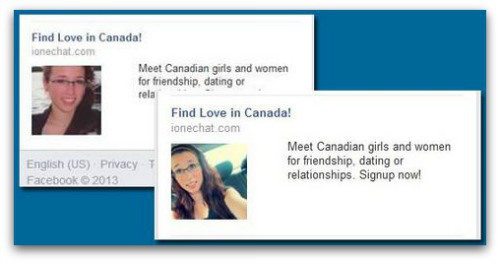
 He has also heard that a spokesperson from the dating site has apologized for the incident, along with Facebook, which removed the ad “with un-Facebook-like speed,” he wrote.
He has also heard that a spokesperson from the dating site has apologized for the incident, along with Facebook, which removed the ad “with un-Facebook-like speed,” he wrote. 