Prolexic Shares Best Practices for Protecting E-Commerce Sites Against Q4 DDoS Attacks
HOLLYWOOD, FL – (September 19, 2013) – Prolexic, the global leader in Distributed Denial of Service (DDoS) protection services, announced today that it has released a number of best practices that firms operating e-Commerce websites can implement to reduce the impact of cyber attacks.
In a new Executive Series white paper, “Safeguarding e-Commerce Revenues from DDoS Attacks in Q4,” Prolexic advises online retailers to be on high alert for DDoS attacks in Q4. Extended site downtime and the resulting inability to make sales and process online orders during the holiday shopping period, including Black Friday and Cyber Monday, can significantly jeopardize Q4 revenues for e-tailers.
Prolexic expects DDoS attacks against e-Commerce sites to increase in size and intensity this fourth quarter, based on previous attack events noted in the company’s “Q4 2012 Quarterly Global DDoS Attack Report.” In Q4 last year, the most active quarter of the year, Prolexic mitigated attacks that reached more than 50 Gbps directed against clients in e-Commerce, financial services and SaaS markets. The average attack duration was 32.2 hours, a crippling duration in e-Commerce.
“Past experience shows that online retailers must take seriously the increased threat of DDoS and other cyber-attacks during the holiday shopping season,” said Stuart Scholly, president of Prolexic. “Online shoppers have many options, and if they can’t readily conduct business with you, they will quickly turn to competitors instead. This white paper offers insight about the current DDoS threat landscape and provides a clear blueprint for building a stronger DDoS defense, so you can avoid downtime and support sales.”
This executive series white paper addresses the escalating cyber threats targeting e-Commerce sites and recommends best practices for protecting online retailers against loss of sales and revenue, damaged brand reputation, and reduced customer confidence due to DDoS. Prolexic also reveals key warning signs that a website could be targeted for a denial of service attack and concludes with best practice recommendations for making DDoS mitigation a part of a disaster recovery plan. The white paper is available to the public at www.prolexic.com/safeguarding.
The white paper also provides a link to PLXplanner, Prolexic’s free, online DDoS protection and planning tool. PLXplanner helps e-Commerce sites understand their vulnerabilities for a denial of service attack, as well as provides recommendations on how to strengthen their DDoS defense. PLXplanner is available at www.prolexic.com/plxplanner.
About Prolexic
Prolexic Technologies is the world’s largest, most trusted Distributed Denial of Service (DDoS) protection and mitigation service provider. Able to absorb the largest and most complex DDoS attacks ever launched, Prolexic protects and restores within minutes mission-critical Internet-facing infrastructures for global enterprises and government agencies. Ten of the world’s largest banks and the leading companies in e-Commerce, SaaS, payment processing, travel, hospitality, gaming and other industries at risk for DDoS attacks rely on Prolexic for DDoS protection. Founded in 2003 as the world’s first in-the-cloud DDoS mitigation platform, Prolexic is headquartered in Hollywood, Florida, and has DDoS scrubbing centers located in the Americas, Europe and Asia. To learn more about how Prolexic can stop DDoS attacks and protect your business, please visit prolexic.com, and follow us on LinkedIn, Facebook, Google+ and @Prolexic on Twitter.
Article source: http://www.darkreading.com/vulnerability/prolexic-shares-best-practices-for-prote/240161539
 Ahoy, me hearties!
Ahoy, me hearties! So, think of it as an extension of
So, think of it as an extension of  Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage.
Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage. With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
 US citizens are now one step closer to being able to do (more or less) what they want with their gadgets – at least as far as choosing a wireless carrier goes.
US citizens are now one step closer to being able to do (more or less) what they want with their gadgets – at least as far as choosing a wireless carrier goes. 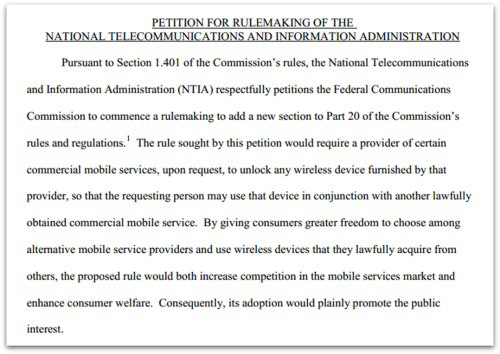
 In 2012, EFF actually asked for – and won – exemptions for jailbreaking or rooting mobile phones to run unapproved software. That didn’t extend to tablets, however.
In 2012, EFF actually asked for – and won – exemptions for jailbreaking or rooting mobile phones to run unapproved software. That didn’t extend to tablets, however.