Telly chef Jamie Oliver in embarrassing infection double shocker
Mockney chef Jamie Oliver is a wizard at cooking – but his website team isn’t exactly cordon bleu standard, as his webpages have put steaming dishes of malware back on the menu.
Last month, researchers at security firm Malwarebytes found jamieoliver.com was hosting an exploit kit that could dish up malware to visitors looking for the latest ways to dazzle their dinner guests.
“The team at jamieoliver.com found a low-level malware problem and dealt with it quickly,” the chef’s representatives told Malwarebytes at the time. “The site is now safe to use. We have had only a handful of comments from users over the last couple of days, and no-one has reported any serious issues.”
It appears the dot-com’s web security team need a few lessons in how to do their jobs. Malware is back on the site, and this time it’s even digitally signed as a Windows executable.
That’s not pukka, mate
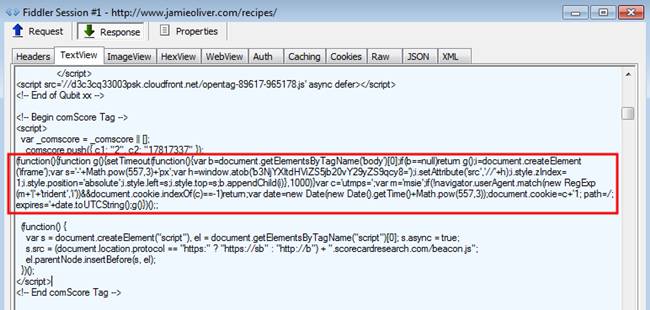
Malwarebytes found the malicious code disguised within the HTML for the site’s comScore analytics tag. It is also digitally signed with a certificate from Just Great Software, although the certificate is now expired.
“This is basically the same structure as we observed in the previous hack, which leads us to believe this is the same infection that was not completely removed or perhaps that a vulnerability with the server software or Content Management System (CMS) still exists,” said Jérôme Segura, a senior security researcher at Malwarebytes.
“This example of a popular and legitimate site is a stern reminder that there is no such thing as a ‘safe’ site anymore. We have documented time and time again on this blog malicious advertisements as well as site hacks that affect well-known brands just the same as smaller sites.”
El Reg contacted Jamie Oliver’s press office for comment but we have yet to hear back. They’re probably off supping beer and indulging in cockles in vinegar. In the meantime, treat the site with the same caution you’d use with day-old sushi. ®
Sponsored:
Designing and building an open ITOA architecture
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2015/03/13/jamie_oliver_malware/