Banking apps: insecure and badly written, say researchers
A guide to transactional email
Security researchers IO Active are warning that many smartphone banking apps are leaky and need to be fixed.
Testing 40 iOS-based banking apps from 60 banks around the world, the research summary is pretty nerve-wracking:
- 40 per cent are vulnerable to man-in-the-middle attacks, because they don’t validate the authenticity of SSL certificates presented by the server;
- 20 per cent lacked “Position Independent Executable (PIE) and Stack Smashing Protection enabled”, which IO Active says is used to help mitigate memory corruption attacks;
- Half the apps are vulnerable to cross-site-scripting (XSS) attacks;
- Over 40 per cent leave sensitive information in the system log; and
- Over 30 per cent use hard-coded credentials of some kind.
Most worrying, however, are a couple of 90 per cent statistics: the number of apps that included non-SSL links, and the number that lack jailbreak detection. Even those with detection could still be installed: “All of the applications could be installed on a jailbroken iOS device. This helped speed up the static and black box analysis”, writes IO Active’s Ariel Sanchez.
By including non-SSL links in the apps, Sanchez says, an attacker could “intercept the traffic and inject arbitrary JavaScript/HTML code in an attempt to create a fake login prompt or similar scam.”
“Moreover, it was found that 50% of the apps are vulnerable to JavaScript injections via insecure UIWebView implementations. In some cases, the native iOS functionality was exposed, allowing actions such as sending SMS or emails from the victim’s device,” he continues.
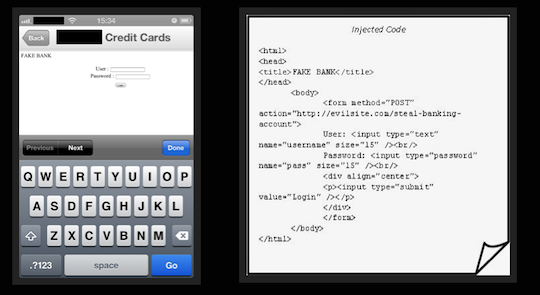
This UIWebView implementation allows a false HTML form to be injected. Source: IO Active
The IO Active post also details a number of other information leaks, including unencrypted data stored in sqlite databases, and information like IP addresses and application paths that could let a determined and skilled attacker draw inferences about the server-side infrastructure the app is talking to.
The research only looked at the client side, Sanchez states, and where possible, IO Active notified banks of the vulnerabilities he identified. ®
Quick guide to disaster recovery in the cloud
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2014/01/13/banking_apps_insecure_and_badly_written_say_researchers/