Chrome is the most secured browser
Google Chrome offers more protection against online attacks than any other mainstream browser, according to an evaluation that compares exploit mitigations, malicious link detection, and other safety features offered in Chrome, Internet Explorer, and Firefox.
The 102-page report, prepared by researchers from security firm Accuvant, started with the premise that buffer overflow bugs and other security vulnerabilities were inevitable in any complex piece of software. Rather than relying on metrics such as the number of flaws fixed or the amount of time it took to release updates, the authors examined the practical effect protections included by default in each browser had on a wide class of exploits.
Their conclusion: Chrome is the most secured browser, followed closely by Microsoft IE. Mozilla’s open-source Firefox came in third, largely because of its omission of a security sandbox that shields vital parts of the Windows operating system from functions that parse JavaScript, images and other web content.
“We found that Google Chrome did the most sandboxing,” Chris Valasek, who is a senior research scientist for Accuvant, told The Register. “It restricted the movements more than any other browser. Internet Explorer came up a close second because it implemented a sandbox where you could do certain things but you were allowed to do more things than you could in Chrome. Lastly, Firefox came in last because it didn’t implement a sandbox yet.”
The report was commissioned by Google, but the authors insist they had complete autonomy in deciding what metrics to use and what conclusions they made. The researchers have released more than 20MB worth of data, software tools, and methodology so peers may review or build upon the research. The study focused solely on the security offered by Chrome, IE, and Firefox, which when combined account for more than 93 percent of web users, according to the report. All three browsers tested were run on Windows 7.
Their finding is backed up by anecdotal evidence, as well. Chrome has emerged unscathed during the annual Pwn2Own hacker contest for three years in a row, something no other browser entered has done. Reports of in-the-wild exploits that target the browser are also extremely rare.
Not all sandboxes are equal
In much the way traditional sandboxes prevent sand from mixing with grass on a playground, security sandboxes isolate application code inside a perimeter that’s confined from sensitive OS functions. By placing severe restrictions on an application’s ability to read and write to the hard drive and interact with other peripheral resources, sandboxes are designed to lessen the damage attackers can do when they successfully exploit a vulnerability in the underlying code base.
The so-called token in the Chrome sandbox, for instance, doesn’t allow browser processes to access files outside of an extremely limited set of directories. It also forbids them from creating connections known as network sockets to communicate directly with servers over the internet. The sandbox in IE, by contrast, allows browser resources to read almost all parts of a hard drive and puts few restrictions on the creation of network sockets, the researchers said.
As a result, attackers who exploit a vulnerability in the Microsoft browser will have an easier time accessing contacts, documents, and other data stored on the hard drive of a targeted computer and uploading it to a command and control server.
“The Google Chrome token is far more restrictive,” said Accuvant Chief Research Scientist Ryan Smith, who compared tokens to a driver’s license that spells out what vehicles a holder is permitted to drive and other conditions, such as whether eyeglasses are required. “It’s more like a learner’s permit, whereas the Internet Explorer token is more like a Class C regular driver’s license.”
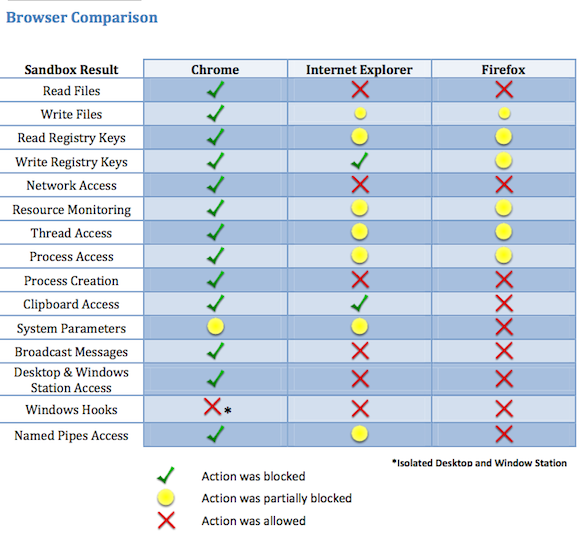
The researchers analyzed each browser’s ability to read files, write files, and perform 13 other actions. As indicated in the graphic below, Chrome blocked all but two of them. Of those, one known as “system parameters” was partially blocked. IE, meanwhile, completely blocked only two actions, and partially blocked seven more actions. Seven additional actions, including the ability to read files, access networks, and create processes, were completely unrestricted.
In last place was Firefox, which allowed nine actions and partially blocked the remaining six actions.
Side-by-side comparison of sandbox protections in Chrome, IE, and Firefox. Source Accuvant (click to enlarge)
Next page: Sin of omission
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2011/12/09/chrome_ie_firefox_security_bakeoff/