Google takes aim at deceptive advertising of Play Store apps
 Google announced updates to its developer policies for the Play Store app market that will hopefully help the company crack down on the worst abuses of some Android apps, including deceptive and potentially harmful behavior without the user’s awareness.
Google announced updates to its developer policies for the Play Store app market that will hopefully help the company crack down on the worst abuses of some Android apps, including deceptive and potentially harmful behavior without the user’s awareness.
Through periodic updates to its policies, Google is attempting to clean up its Android market and punish developers who try to work around the rules against pornography, gambling, spyware, adware and malware – even as the number of apps in the Play Store has surged past one million with more added every day.
Although the policy changes won’t stop developers from cramming free apps with advertising, the rules Google announced 28 March 2014 make several adjustments to Google’s policy on what typically we would call adware.
The biggest change to the policies is the addition of an App Promotion policy, which bans ad behavior such as silently downloading apps without user consent, and ads that use misleading pop-up warnings including simulated system, service, or app notifications or alerts.
In an email to developers and in a post on Google Plus, Google notified developers that they have until 12 April 2014 to comply, or they risk having their apps bounced from the store.
PUAs, aggressive pop-up ads, and drive-by downloads
The Play Store developer policies now explicitly ban certain types of advertising behavior within apps and on advertising networks; misleading app descriptions on Play Store; silent downloads of the app without consent; and “push” advertising in the form of SMS text messages.
Apps published on Google Play may not directly or indirectly engage in or benefit from the following behavior:
- Promotion via deceptive ads on websites, apps or other properties, including simulated system, service, or app notifications or alerts.
- Promotion or install tactics which cause redirection to Google Play or the download of the app without informed user action.
- Unsolicited promotion via SMS services.
It is your responsibility to ensure that no ad network or affiliate uses such methods to direct users to pages that make your app available for download.
These characteristics may not exactly qualify the apps as malware, but they sure do have the signs of a potentially unwanted app (PUA).
Our SophosLabs threat researchers have identified thousands of PUAs – we’ll look at three of them that use some of these abusive promotional tactics.
Plus, check out the security tips at the end of this article so you know how to avoid malware and PUAs.
→ There’s no agreed-upon definition of PUAs, which are sometimes called PUPs for potentially unwanted program. Although they are not classified as malware, PUAs may nevertheless introduce risks for security and privacy and can negatively affect a device’s usability. SophosLabs researchers Vanja Svajcer, who contributed to this article, and Sean McDonald, explore this topic in their technical paper Classifying PUAs in the Mobile Environment (PDF).
→ A special thanks to Ferenc László Nagy of SophosLabs Hungary for providing research for this article.
Clean Master
Clean Master is a wildly popular download, ranked number one in Google Play’s Tools category, according to TechinAsia.com, and is promoted as an “Android cleaner and optimizer,” including protection against malware.
 Despite its popularity, ads promoting Clean Master manipulate Android users with deceptive tactics when browsing websites within the app’s advertising framework.
Despite its popularity, ads promoting Clean Master manipulate Android users with deceptive tactics when browsing websites within the app’s advertising framework.
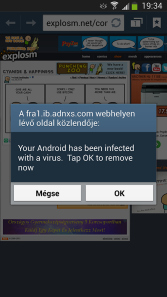
Ferenc László Nagy of SophosLabs Hungary has captured some pop-up ads that lead to Clean Master, warning you that your device has been infected with a virus.
In the screenshot at right, you see that this particular pop-up ad says:
Your Android has been infected with a virus. Tap OK to remove now
On the buttons it says in Hungarian “Mégse” (Cancel) and “OK.”
Only if you press “OK” the ad redirects you to the download of the Clean Master app, and does not “remove” the (fake) virus as the ad claims.
According to the website Stayprotected.com, several other ads promoting Clean Master resemble warning screens informing you that your battery is running low due to “potential viruses” on the device.
Mobogenie
Mobogenie helpfully bills its apps as “Virus-free” – but that hasn’t stopped the developer from using deceptive practices including drive-by downloads of the Mobogenie app that could make it a PUA in Google’s eyes.
After receiving numerous complaints about automatic downloads of the Mobogenie app, the company wrote a message to users on the Play Store declaring that it is working to fix the problem with one of its “promotional partners.”
Dear Users,
Recently we have understood that some of our users have been troubled by the automatic download of Mobogenie on to their Android Phones.
While it has never been our intention to spam any user, we would like to apologise to them for the same. Having learnt that there was a technical issue with one of our promotional partners, we are trying our best to fix it at the earliest.
Team Mobogenie keeps a close eye on all its promotions, and recommends the download of Mobogenie application only from reliable sources such as Google Play, Mobogenie.com and other partner networks. We ensure that there shall be no more inconvenience caused to any Android user in future.
If you face this Problem or anything similar Issues again, Please write to us at [email protected] with the below details.
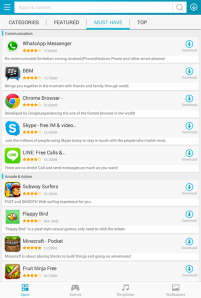 In the screenshot of the Mobogenie Market app shown at right, you see what the Mobogenie Market’s “Must Have” app screen looks like. (Click on the image for a larger version.)
In the screenshot of the Mobogenie Market app shown at right, you see what the Mobogenie Market’s “Must Have” app screen looks like. (Click on the image for a larger version.)
Naked Security writer Paul Ducklin commented that the market contains knock-off versions of popular apps, including the no-longer-available Flappy Bird game.
Much like the mangled English of the Mobogenie to-users letter quoted above, the descriptions of the apps within the market are also rife with spelling and grammatical errors.
Despite this rather glaring evidence of poor attention to detail by Mobogenie – which is, after all, not just an app vendor but an entire, alternative app market – the product is used by many millions of people, having been downloaded more than 10 million times from the Play Store alone.
Mobogenie users might want to think twice about playing outside Google Play.
 Android Armor
Android Armor
Android Armor is an anti-virus app closely tracked by SophosLabs researcher Vanja Svajcer.
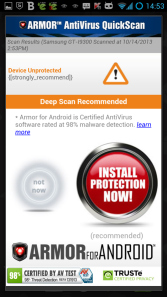
Vanja shared some ad screenshots that show how Android Armor violates Google’s developer policies with misleading claims that could trick the user into believing they need the app to prevent malware infection.
One ad in particular with a giant red button to download the app (see screenshot) makes a false claim that the device is not protected, although our test Android was fully protected with several security products, including Sophos Mobile Security.
Tips to avoid malicious or unwanted apps
1. If it looks suspicious, it probably is. Don’t click on ads that claim to find malware on your device or use big red Alerts! – as you don’t know what might be lurking behind it.
2. Use common sense when it comes to permissions. If an app requests access to your contacts or device settings, it should explain why. Don’t hesitate to refuse access if you’re not fully convinced.
3. Third-party app stores carry the greatest risk. Google Play isn’t perfect: malware-infected apps and PUAs evade its filters. But many third-party app stores are far riskier. You should avoid file-sharing sites offering free versions of apps that normally require payment. Many of these apps have been cracked and infected.
4. Use consumer reviews as guidance. Multiple negative reviews or warnings about app misbehavior deserve to be taken seriously.
5. Protect your data, protect your phone. Use encryption to scramble data stored on your device or on cloud-based storage services. That way, if your data leaks out or you lose your smartphone or tablet, your confidential information never falls into the wrong hands.
6. Get reliable malware protection for your Android. You always want to have anti-virus protection on your Windows PCs and Macs, but don’t forget your Android devices – they need protection too.
Sophos Mobile Security for Android gives you anti-virus protection, including detection and blocking of adware and PUAs, loss and theft protection, plus a handy security and privacy advisor.
You can download it for free from the Google Play Store.
Article source: http://feedproxy.google.com/~r/nakedsecurity/~3/u31PUeuS_kg/