Russian government spies extracted NSA exploits from a US government contractor’s home PC using Kaspersky Lab software, anonymous sources have claimed.
The clumsy snoop broke regulations by taking the classified code, documentation and other materials home to work on using his personal computer, which was running Kaspersky’s antivirus, sources told the Wall Street Journal. It is alleged Kremlin hackers exploited the security package in one way or another to identify those sensitive files and exfiltrate them.
In effect, it means the Russian government has copies of the NSA’s tools used to exploit vulnerabilities in computer systems and equipment to spy on other nations and targets. It also means Russia can turn the cyber-weapons on American corporations, government agencies and other networks, and steal secrets, cause merry havoc, and so on.
The theft, reported today, is said to have occurred in 2015, but apparently wasn’t discovered until earlier this year. The allegedly stolen NSA code and dossiers sound an awful lot like the Shadow Brokers archive of stolen agency spyware. The brokers’ pilfered exploits dates back to 2013, though.
And this case is not thought to be related to the former Booz Allen Hamilton contractor Harold Thomas Martin III who stashed classified NSA materials at his home to study. Martin was indicted in February and faces prison time for removing top-secret files from his employer’s workplace, if convicted. He denies any wrongdoing.
“Whether the information is credible or not, NSA’s policy is never to comment on affiliate or personnel matters,” an NSA spokesperson said.
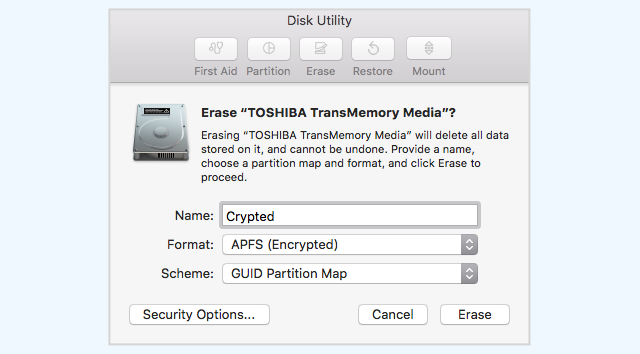
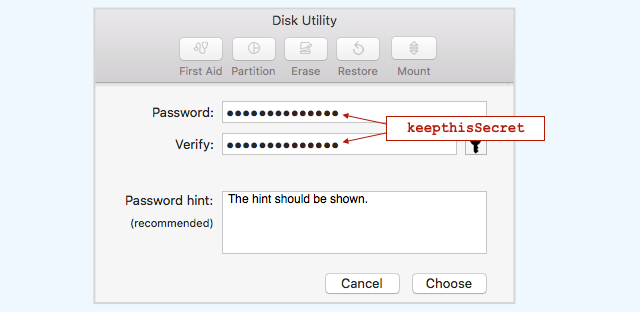
Like almost all security software, Kaspersky’s software scans files on computers to look for anything matching known malware, or programs that behave in a way that looks like malicious code. It may be that the antivirus package sent the contractor’s NSA code back to a cloud service to inspect, which set off internal alarms and attracted the attention of Russian spies, or the product was tampered with to open a backdoor to the PC, or the software was remotely exploited to gain access.

Homeland Security drops the hammer on Kaspersky Lab with preemptive ban
READ MORE
The WSJ’s sources don’t say if Kaspersky was actively involved in helping hack the contractor’s computer, or if President Putin’s spies exploited vulnerabilities in the security software to silently swipe the exposed documents. And there are a lot of exploitable holes in antivirus packages for hackers to abuse.
It is also possible, under Russian law, the Kremlin instructed staff within Kaspersky to hijack the mark’s computer and extract its contents. The software maker is denying any involvement.
“Kaspersky Lab has not been provided any evidence substantiating the company’s involvement in the alleged incident reported by the Wall Street Journal on October 5, 2017, and it is unfortunate that news coverage of unproven claims continue to perpetuate accusations about the company,” the Moscow-based biz told The Register in a statement.
“As a private company, Kaspersky Lab does not have inappropriate ties to any government, including Russia, and the only conclusion seems to be that Kaspersky Lab is caught in the middle of a geopolitical fight.
“Kaspersky Lab products adhere to the cybersecurity industry’s strict standards and have similar levels of access and privileges to the systems they protect as any other popular security vendor in the US and around the world.”
The organization’s founder Eugene Kaspersky was more blunt, tweeting the following before today’s revelations hit the ‘net:
Kaspersky has repeatedly offered up its source code for officials to review since allegations that it was working with Russian intelligence surfaced a year or so ago. No evidence has ever been made public about such claims, and that didn’t stop the US government banning Kaspersky code from federal computers last month. American box-shifter Best Buy followed suit.
“It’s a lot harder to beat your opponent when they’re reading your playbook, and it’s even worse when someone on your team gives it to them. If these reports are true, Russia has pulled that off,” said US Senator Ben Sasse (R-NE), who is on the Senate Armed Services committee.
“The men and women of the US Intelligence Community are patriots; but, the NSA needs to get its head out of the sand and solve its contractor problem. Russia is a clear adversary in cyberspace and we can’t afford these self-inflicted injuries.”
Matthew Hickey, cofounder of British security shop Hacker House, told The Register that Kaspersky could well be blameless and the security software was simply doing its job. The Russian software maker has been detecting NSA malware since 2014, and this could be where the connection lies. The antivirus may have identified Uncle Sam’s powerful exploit code on the home PC, and flagged it up, possibly all the way to the FSB, Russia’s security services.
“It’s likely that the Kaspersky detection of NSA tools was somehow responsible for FSB targeting the contractor’s home computer but it doesn’t mean the company was complicit,” Hickey said.
“Kaspersky have detected many of the NSA tools being used in the wild, the FSB would surely know that, and target the company for that reason alone. The Kaspersky statement holds no punches and makes it clear they don’t cooperate with governments. I’m inclined to believe them, their software is top grade at detection of new threats, and is notoriously difficult to bypass.”
He pointed out that the alternative is that Kaspersky deliberately backdoored its own software, and handed over the keys to Putin”s snoops, putting billions of dollars of business at risk to do a favor for Russian intelligence. Occam’s razor would suggest this is unlikely.
Meanwhile, cybersecurity expert Matt “Pwn all the Things” Tait said the focus should be on the embarrassing claims that yet more dangerous NSA tools have escaped Uncle Sam’s highly secretive surveillance agency:
Senator Jeanne Shaheen (D-NH), one of Kaspersky’s most vocal critics in Congress, has few doubts. In a strongly worded statement, she condemned the company and called for the Trump administration to declassify and release the evidence it has in this case.
“The strong ties between Kaspersky and the Kremlin are extremely alarming and have been well documented for some time,” she said today. “It’s astounding and deeply concerning that the Russian government continues to have this tool at their disposal to harm the United States.” ®
PS: The Washington Post says the contractor was a US citizen born in Vietnam, and worked for the NSA’s ace hacking team, Tailored Access Operations. He was fired in 2015, and is under a federal investigation.
Sponsored:
The Joy and Pain of Buying IT – Have Your Say
Article source: http://go.theregister.com/feed/www.theregister.co.uk/2017/10/05/anonymous_report_russian_spies_used_kaspersky_lab_software_to_steal_nsa_secrets/