Q&A: Security In The Spotlight At Interop
Security and networking professionals are gearing up for the Interop show in New York next month. As we ramp into the show, Dark Reading caught up with John Pironti, chair of both the Risk Management and Security track as well as co-chair of the Applications and Collaboration track. Pironti is president of security consultancy IP Architects, LLC and is also an active member of ISACA.
 Click here for more articles from Dark Reading.
Click here for more articles from Dark Reading.
Click here to register to attend Interop.
Dark Reading: John, tell us a little bit about some of the security themes you have helped to develop with the programming in the Risk Management and Security track at Interop this year.
Pironti: Not like a unlike at ISACA, at Interop we’ve really been trying to push the theme and kind of move the bar forward for security professionals to become more risk and security professionals and to be more embracing of a threat- and vulnerability-based and risk-based approach, not a technology-based approach to security. We want people to appreciate that, in some cases, it’s actually be better to be the trusted advisor than it is to be the guy with the hammer.
Dark Reading: Which is kind of makes Interop the perfect audience to bring that message to, considering how many security professionals come from the networking world, right?
Pironti: Yeah. The good news there is that we have a lot of maturity because of that. Network security is probably the area of security that is the most mature and has the most specialists available. But we’d like to start pushing lots of data conversations.
Networking, and technology generally, is really a vessel. WE have all these other angles we’re working on and all these other requirements at the business level that we have to address. So we’re trying to help that professional broaden their horizons and try to understand what their customers and management teams are struggling with.
One theme we’re trying to move forward is visibility, because you can’t protect what you don’t know. And then, really moving away from using the word risk too easily and really trying to appreciate what risk really means to the business person and what the security professional believe risk to be. These are usually two very different things.
Dark Reading:So better business context for risk?
Pironti:So a security professional can understand all the possibilities and probabilities of a threat and a vulnerability of a technology or of a concept. In order to factor in what’s a risk to the business, you have to have consciousness of things like operational risk, strategy risk, financial considerations, HR considerations, and legal considerations. We need to work with them to understand, how to we get on the same language page so when I say something’s a risk it’s couched in a way of saying it’s an information risk, but it has a potential impact on your business process
Dark Reading: That ties into some conversations we’ve had with people about generally having it risk rolled up into enterprise risk management? What are you seeing there?
Pironti: ISACA and I have been having that conversation for a while. Maybe we separate IT security operations from information risk management. But they are two things that are very heavily integrated and they should talk to each other and deal with each other regularly. Let the technology group still maintain the controls, and understand how we’re going to meet those controls. But let the risk group define what the control objectives need to be.
[Do you see the perimeter half empty or half full? See Is The Perimeter Really Dead?.]
Dark Reading: Looking at general trends, what would you say security people should be paying attention to that will be on the Interop radar, trends like software defined networking (SDN)?
Pironti: I think SDN is great. I think we’re at the fun time talking about SDN. At Interop you have networkers and we love this stuff. This is our bread and butter.
I think that like other standards we’ve had, we’re high in the hype cycle right now. We still have to wait for the standards to play. It is a logical step forward, though, from a provisioning and maintenance and management perspective. But I don’t think it’s going to replace overnight what we do for traditional networking, or traditional operations or application management or things of that nature.
Every couple of years we come up with something new that is going to change the world. SOA, cloud—this is the third time we’re trying cloud, we just keep calling it something different, NAC. Remember in 2001 and 2002, we were all going to do NAC? Now NAC is back. And it actually makes sense, finally. So I think the security professional needs to keep an eye on how data is becoming more pervasive and how it’s being extended beyond their boundaries and what that means. As well as understanding what are the capabilities of some of these new trends that are coming online and how they’ll impact not only their internal operations but how they interact with other organizations.
Have a comment on this story? Please click “Add Your Comment” below. If you’d like to contact Dark Reading’s editors directly, send us a message.
Article source: http://www.darkreading.com/risk/qa-security-in-the-spotlight-at-interop/240161571
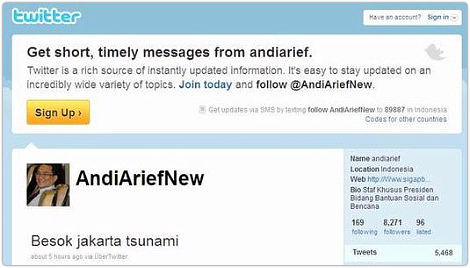
 If you live in the UK and listened to the radio earlier this week, you might have heard
If you live in the UK and listened to the radio earlier this week, you might have heard  And there’s the problem of maintaining and disseminating the list so it can be used in real time: that list would be a prized possession for cybercrimimals.
And there’s the problem of maintaining and disseminating the list so it can be used in real time: that list would be a prized possession for cybercrimimals.
 US citizens are now one step closer to being able to do (more or less) what they want with their gadgets – at least as far as choosing a wireless carrier goes.
US citizens are now one step closer to being able to do (more or less) what they want with their gadgets – at least as far as choosing a wireless carrier goes. 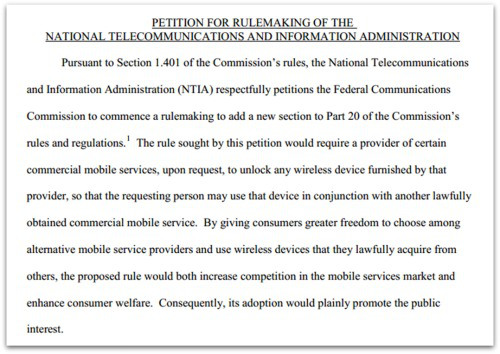
 In 2012, EFF actually asked for – and won – exemptions for jailbreaking or rooting mobile phones to run unapproved software. That didn’t extend to tablets, however.
In 2012, EFF actually asked for – and won – exemptions for jailbreaking or rooting mobile phones to run unapproved software. That didn’t extend to tablets, however.  Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage.
Fire sprinklers and clearly marked escape routes are a great way to save lives in the event of fire. But smoke alarms save both life and property, and they do so at a much earlier stage. With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
With just a little training and occasional reinforcement, your users will recognize the seductive signs of phishing and malware knocking at the door, from the clumsy and prurient (Check out these hot babes), to the falsely authoritative (You need to update Adobe Flash).
 Happy day, USA: When we click “Like” on Facebook, we are now constitutionally protected from getting fired!
Happy day, USA: When we click “Like” on Facebook, we are now constitutionally protected from getting fired!